Alexa I Encountered an Error When Trying Reach Salesforce Please Try Again Later
Hello everyone, today we take another post from Intune Support Engineer and resident Jamf expert Shonda Hodge. Shonda already published detailed steps on getting Jamf integration configured here, and today she follows that up with an article on how to troubleshoot integration if you encounter any problems. Special thanks to Bryce Carlson (Sr. Support Engineer @Jamf), Camden Webster (Sr. Back up Engineer @Jamf),Lucas Lenard (Back up Engineer I @Jamf) and Geoff Root (Test Engineer I @Jamf) who worked closely with Shonda to get this commodity created.
NOTE If you run into problems with the integration of Jamf and Intune, delight open up a ticket with Jamf first. They will propose whether a case needs to be opened with Microsoft.
=====
If your organization uses Jamf Pro to manage macOS devices, yous can use Microsoft Intune compliance policies with Azure Agile Directory conditional access to ensure that devices in your organization are compliant earlier accessing company resource. Jamf does this by allowing admins to sync their Mac inventory information with Intune and the Microsoft Cloud. This inventory information can then be analyzed by Intune'south compliance engine to generate a report, then combined with intelligence about the user'southward identity, enforce conditional access via European monetary system. If the Mac device is compliant with the conditional admission policies configured, it volition be immune admission to the protected company resource.
Device Registration Explained
Device registration is the procedure in which a device'due south identity is established in AAD. It uses the public-private central infrastructure, and on the device/client side information technology'southward referred to equally workplace joined (WPJ)/domain-joined (DJ)/Azure Advertisement-joined (AADJ) whereas on the server side it is referred to every bit Azure Device Registration Service (ADRS or simply DRS). This device identity is needed for Intune registration.
Notes on MacOS Authentication and Registration
- The WPJ country is stored in Login keychain.
- Login keychain admission is needed to complete device hallmark on MacOS.
- Login keychain typically has the aforementioned password as the MacOS sign-in countersign, nevertheless it could also have a dissimilar password.
- The Intune Company Portal app is required to practice device registration, which occurs during JamF
- There is no broker on MacOS. All customer apps using ADAL (Azure Agile Directory Hallmark Library) can do device AuthN, simply users will run into KeyChain admission countersign prompts.
Note: AuthN primarily deals with user identity: who is this person? Is she who she says she is?
Troubleshooting Intune Registration for Jamf-managed devices
It's important to notation that the Intune Company Portal app must be launched from the Jamf Self Service app; if not the device volition not be properly registered. When troubleshooting registration problems, start past gathering the post-obit information:
- Azure AD Device ID
- Company Portal logs (instructions are here)
- The sysdiagnose log archive from macOS (will comprise jamfAAD procedure logs). To generate a sysdiagnose, run the post-obit command from the enrolled Mac device with your desired save location (e.g. /Desktop for the logged in users' desktop):
sudo sysdiagnose -f /path/to/desired/save/location
- To view just jamfAAD logs on a Mac for quick troubleshooting, run this command on the Mac to go the last 30 minutes of data:
log show --predicate 'subsystem CONTAINS "jamfAAD"' --last 30m
Here'southward an example of a Company Portal log showing successful Intune registration:
2019-01-23 17:32:fifteen.119 INFO com.microsoft.ssp.workplaceJoinSdk TID=27 WorkplaceJoinManager.swift: 796 (workplaceClient(_:logMessage:)) INFO: -[WorkPlaceJoin saveWorkplaceJoinStateToDevice:certificatePerferredPaths:correlationId:error:] [Line 1519][2019-01-23 17:32:15 +0000]Successfully completed device registration
2019-01-23 17:32:15.120 INFO com.microsoft.ssp.workplaceJoin TID=27 WorkplaceJoinManager.swift: 475 (didCompleteJoin()) In-app workplace join succeeded.
2019-01-23 17:32:xv.159 INFO com.microsoft.ssp.enrollment TID=1 EnrollmentInProgressPaneViewController.swift: 111 (handleEnrollmentStateChange()) WPJ only enrollment complete, go to checklist page
"[\"ChassisType\": \"Desktop\", \"IsExchangeActivated\": \"0\", \"PartnerLocalizedSelfServicePortalName\": \"SelfService\", \"odata.editLink\": \"https://fef.msua06.manage.microsoft.com/StatelessIWService/Devices(guid'8253763b-8b89-4240-bebe-ef60...", \"ExchangeActivationItemEasId\": \"\", \"PartnerName\": \"Jamf\", \"ManagementAgent\": \"JamfClient\", \"LastContact\": \"2019-01-23T17:28:28\", \"Manufacturer\": \"Apple\", \"Nickname\": \"Rechelle\U2019s MacBook Air\", \"OwnerType\": \"0\", \"ApplicationState\": \"https://fef.msua06.manage.microsoft.com/StatelessIWService/Devices(guid'xxxxxxxx-8b89-4240-bebe-ef60...", \"SetHeartBeat\": \"[\"target\": \" https://fef.msua06.manage.microsoft.com/StatelessIWService/Devices(guid'xxxxxxxx-8b89-4240-bebe-ef60... \ "]\", \"Key\": \"xxxxxxxx-8b89-4240-bebe-ef60cccf6e8b\", \"SetRD\": \"[\"target\": \"https://fef.msua06.manage.microsoft.com/StatelessIWService/Devices(guid'xxxxxxxx-8b89-4240-bebe-ef60...", \"ComplianceState\": \"Compliant\", \"CategorySetByEndUser\": \"0\", \"Model\": \"MacBook Air (13-inch Early on 2015)\", \"LastContactNotification\": \"0001-01-01T00:00:00\", \"PartnerSelfServicePortalUrl\": \"jamfselfservice://\", \"CategoryId\": \"[null]\", \"SetOptIn\": \"[\"target\": \"https://fef.msua06.manage.microsoft.com/StatelessIWService/Devices(guid'xxxxxxxx-8b89-4240-bebe-ef60...", \"DeviceHWId\": \"ten:94:BB:C7:3E:70\", \"AadId\": \"xxxxxxxx-8b89-4240-bebe-ef60cccf6e8b\", \"GetManagementState\": \"[\"target\": \"https://fef.msua06.manage.microsoft.com/StatelessIWService/Devices(guid'xxxxxxxx-8b89-4240-bebe-ef60...", \"AppWrapperCertSN\": \"[zip]\", \"CreatedDate\": \"2019-01-23T17:37:03.9872113\", \"PartnerRemediationUrl\": \"jamfselfservice://remediate\", \"RemoteSessionUri\": \"[null]\", \"ManagementType\": \"JamfClient\", \"odata.readLink\": \"https://fef.msua06.manage.microsoft.com/StatelessIWService/Devices(guid'8253763b-8b89-4240-bebe-ef60...", \" IsPartnerManaged\": \"1\", \"OfficialName\": \"Rechelle\U2019s MacBook Air\", \"NoncompliantRules\": \"[]\", \"OperatingSystem\": \"Mac Os Ten\"]"
Tips for troubleshooting registration
Note that when configuring a conditional access policy to work with Jamf and Intune DO Not target the Jamf Native macOS Connector app. This will break registration.
- Ensure that the Company Portal app is existence launched from the Jamf Cocky-Service app. If the Company Portal upgrade dialog box pops up, finish the upgrade and quit the app, then re-launch the Company Portal app from JSS.
- Check Enterprise Applications permissions for Jamf in Azure Advertising. Ensure that only the unmarried permission is listed.
- Check to make certain that the Jamf MacOS connector is listed nether Enterprise Applications in Azure Advertisement. If not, log in to the Jamf console and complete the administrator consent.
- For Macs previously enrolled into Intune, if you want to have them managed by Jamf complete the following:
- Unenroll from Intune.
- Clean up the device from the Azure portal by ensuring that the device is no longer listed nether "All Devices" and "Azure AD Devices".
- Make clean upwardly the Mac past removing all workplace join-related certificates from the Key Chain before switching device management providers.
- For Macs previously managed by Jamf and registered with Intune, it is recommended that you make clean up the device by following steps documented hither: Removing Jamf Components from Computers | Jamf Nation. Be sure to confirm that the device is no longer seen in the Azure portal before enrolling back into the Jamf Pro server and attempting Intune registration over again.
- If a Mac device shows Not registered in the Company Portal app, uninstall and register the device by assuasive Jamf to launch the Company Portal app via policy or Cocky Service policy. In this case you will too see the following in the Company Portal log:
INFO com.microsoft.ssp.application TID=i WelcomeViewController.swift: 253 (startLogin()) Portal launched without WPJ simply arg while account is under partner management
How compliance is evaluated
Jamf Pro sends the inventory attributes listed beneath to Intune for the purposes of compliance evaluation. Be enlightened that there are more attributes that Jamf Pro sends, yet for the purposes of this guide nosotros've only listed those that are used to evaluate compliance. For a complete list of attributes that Jamf Pro sends to Intune, see Jamf Inventory data.
- Jamf Inventory State
- OS Version
- User AAD ID
- # of previous countersign to prevent reuse
- Encrypted (File Vault ii)
- Minimum # of character sets
- Password expiration (days)
- Password Blazon
- Prevent Auto Login
- Required Passcode Length
- Start screensaver after inactivity
- System Integrity Protection
Note: If Mac computers take network accounts (or Mobile Habitation Folder Advertizing accounts), compliance policies dealing with password complexity should not be used within Microsoft Intune as they cannot exist reported correctly from Jamf Pro. Password complexity is enforced by the network account server.
Jamf Pro enforces compliance via the configuration profiles scoped to the macOS device and reports to Intune if the figurer is managed based on the local attributes of the device at the fourth dimension check-in. Intune's compliance engine evaluates inventory information from JamfPro and generates a written report and enforces conditional access via Azure Advertizing.
Fields in Azure that displays compliance information
In Azure -> Microsoft Intune – All Devices, yous will run into the terminal check-in time. Be aware that current last check-in fourth dimension is the fourth dimension Intune received related device inventory data time, non actual MacOS check-in fourth dimension to Jamf. This corresponds to what'southward in the Company Portal app.

Under Azure AD devices, the Compliant field is used to determine whether access to resources will be granted. If the compliant state is No, users volition be blocked from protected company resources.
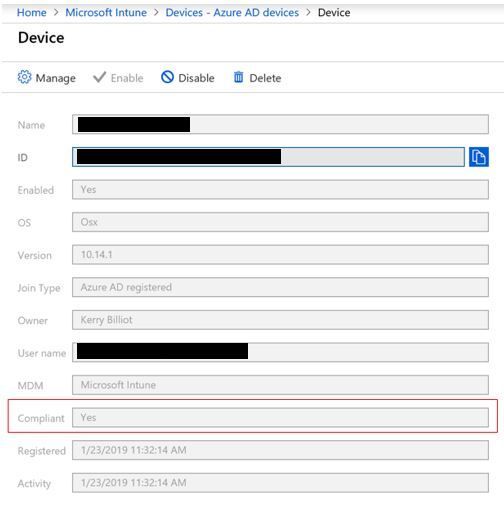
Notation: In Azure -> Microsoft Intune -> Azure AD devices, the Activity field for a device does not have significance for Jamf/Intune compliance evaluation.
Device check-in and compliance
By default, devices bank check-in with Jamf Pro every fifteen minutes. This is configurable in the Jamf Pro console and y'all tin read more on that here. If a device doesn't check-in inside a 24-hour period, Jamf will mark the device as unresponsive. If a device is marked as unresponsive in Jamf, it will not impact the compliance status of a device in Intune. However, if a device is retired in Jamf, Intune will reevaluate the compliance state of the device. Every registered device also has an Azure token. This token is refreshed every 12 hours, and if the token is not able to exist refreshed for 24 hours or more, Jamf volition marker the device as unresponsive and send that status to Intune.
Notation: Enrolled users must log on to correct a non-responsive state. It must be the user who has work-placed joined the account every bit this is the user that has the identity from Intune in their login keychain.
All-time practices for compliance
- To go along Mac computers in compliance, it is recommended that you deploy a configuration profile or a policy in Jamf Pro for each compliance policy created in Microsoft Intune.
- Ensure that the Intune compliance policy aligns with the inventory policy in Jamf.
- On the Jamf side, the admin should add an Inventory policy that finish users tin can use in Self-Service to trigger Jamf Pro to send updated information to Intune on the fly.
- Check if the device shows up in Intune, or when the last check-in time was updated. If hasn't checked in for a long time, cheque the terminal device inventory update on the Jamf Pro side and ensure that the data has been sent to Intune. You can read more on this at the bottom of the following folio: Computer History Information - Jamf Pro Ambassador's Guide | Jamf Product Documentation.
Tips to bring devices back into compliance
- If it has been over 24 hours since the user has logged into the Mac, merely have them log in. You tin also run the following command on the Mac device with the registered user session present:
/usr/local/jamf/bin/jamfAAD gatherAADInfo
- Ensure that the device meets the criteria set in the compliance policy (e.one thousand. password requirements/encryption required). If a device is out of compliance due to encryption requirements, the Company Portal log volition comprise the following message:
"CreatedDate": "xxxx-xx-xxxx:42:09.7465954", "PartnerRemediationUrl": "jamfselfservice://remediate", "RemoteSessionUri": "[[mobile]]", "ManagementType": "JamfClient", "odata.readLink": "https://fef.msua05.manage.microsoft.com/StatelessIWService/Devices(guid'xxxx')", "IsPartnerManaged": "1", "UserApprovedEnrollment": "0", "OfficialName": "[[OfficialName]]", "NoncompliantRules": "[[SettingID": "Device_Encryption_FileVault2Encrypted", "ExpectedValue": "Truthful", "Title": "Turn on device encryption", "MoreInfoUri": "https://go.microsoft.com/fwlink/?linkid=851949", "Clarification": "You must enable full-disk encryption for this device, which wraps your data in a layer of protective code to go on unauthorized people from accessing it. Nosotros recommend you contact your visitor support to enable it.", "RemediationOwner": " user"]"]", "OperatingSystem": "Mac Os X", "RegisterForAppPushNotifications": "["target": "https://fef.msua05.manage.microsoft.com/StatelessIWService/Devices(guid'xxx')/RegisterForAppPushNoti..."
Managing Dried Devices in Azure Advertisement
Ideally, to complete the lifecycle, registered devices should be unregistered when they are not needed anymore. Nevertheless, due to, for example, lost, stolen, broken devices, or OS reinstallations y'all typically have stale devices in your environment. As an IT admin, you probably desire a method to remove stale devices, so that you can focus your resources on managing devices that crave management.
What is a stale device?
A stale device is a device that has been registered with Azure Advert but has not been used to access whatsoever cloud apps for a specific timeframe. Stale devices accept an impact on your ability to manage and support your devices and users in the tenant because:
- Duplicate devices can make it difficult for your helpdesk staff to identify which device is currently agile.
- An increased number of devices creates unnecessary device writebacks increasing the time for AAD connect syncs.
- Equally a general hygiene and to meet compliance, y'all may want to take a make clean land of devices.
For more information on detecting and cleaning up stale devices, please run across the post-obit link: How to manage stale devices in Azure Advert | Microsoft Docs.
FAQ
Under Azure Advert Devices the Mac shows Non-compliant, but under All Devices it shows to be compliant. Which one is accurate?
- The status displayed under Azure Advertizement Devices volition be used for determining access to protected company resources.
My Macs have a password set and my compliance policy requires a passcode, only my devices are still not compliant?
- Exercise you have auto-login set on the Mac (more than on that here: Prepare your Mac to automatically log in during startup - Apple Support)? If so that may exist why as the Mac is not actually secure in spite of having a password set.
Why do I see the device in the Azure Advertizing bract but not in Intune?
- If the device shows up in the Azure AD bract and not Intune, that means Jamf probably didn't get the AAD Device ID. You should see the AAD device ID in the Jamf Pro console. If you do not, that likely means that the Jamf AAD app wasn't successfully run (or didn't complete successfully) so the user should run the device registration policy from Jamf Self Service over again.
If I have a blank compliance policy assigned to my Mac devices, how does Intune evaluate compliance?
- Blank compliance policy (a policy that has no setting) is not beingness calculated as of at present. The device will remain as Unknown.
If a device has not communicated Jamf in over 24 hours, how practice I bring it back into compliance?
- Log into the Mac as the user who registered with Intune. The user's login keychain contains the identity needed to confirm compliance. You tin also trigger the post-obit command from the Mac device with the registered user session present to expedite that process:
/usr/local/jamf/bin/jamfAAD gatherAADInfo
How long does a device have to remain in an unresponsive country before Jamf codes it equally Unmanaged?
- A device that remains in an unresponsive state for over 30 days will be marked as unmanaged past Jamf.
Can you lot force device check-in from Intune? If so, how do you do information technology?
- Currently this is not possible as Jamf is responsible for providing the country of the device. Users should use the Self- Service app for device cheque-in via an Inventory policy for immediate results.
What ports need to exist open for Jamf and Intune to work properly?
- Intune: Port 443
- Apple: Ports 2195/2196/5223 (for Push button notifications to Intune)
- Jamf: P ort 80, 5223
Note: Exist sure to let outbound connections to, and redirects from, Apple's 17.0.0.0/8 block over TCP port 5223 / 443 from all client networks, and on ports 2195 and 2196 from Jamf Pro servers to make sure APNS will part correctly on your network.
Intune reference : Network requirements and bandwidth details for Microsoft Intune | Microsoft Docs
Jamf reference : Network Ports Used by Jamf Pro | Jamf Nation
What causes an Azure AD ID to exist reflected as "Deactivated" in Jamf?
- Typically you will see this after 30 days of inactivity.
If I have an on-premise instance of Jamf and I desire to add a cloud instance of Jamf, can I have both linked to Azure at the same time?
- No. Intune just supports one Jamf connector per tenant in Azure.
If I encounter an issue with my Jamf-managed device registered with Intune and I need assistance, what should I do?
- If you run across issues with the integration of Jamf and Intune, please open up a ticket with Jamf starting time . They volition suggest whether a example needs to exist opened with Microsoft. If a case needs to exist open with Microsoft, delight accept the following information available:
-
The UPN of the affected user(south)
-
The AAD Device ID
-
Company Portal logs
-
Screenshots of compliance/provisional access policies from Intune and screenshots of Jamf configuration profiles (compliance settings specifically)
-
Known issues/solutions
When configuring Jamf with Intune, the following error bulletin appears when trying to confirm settings from the Jamf console:
Graph API Access Token cannot be retrieved
This typically occurs is there is a proxy or firewall blocking required ports. Check the ports listed above.
When configuring Jamf with Intune, the following error message appears:
Graph API Admission Token cannot be retrieved
The Jamf Pro Server log also contains a 401 fault when the connection to Graph is attempted:
[ConditionalAccessHTMLResponse] - Could not enable provisioning
com.jamfsoftware.conditionalaccess.provisioning.InvalidResponseStatusException: Status code 401
This can occur if y'all did not input your App ID correctly on the Device compliance - Partner device direction page. Input and save the correct App ID to resolve this issue.
When trying to register a Jamf enrolled device with Intune, the post-obit message is seen afterwards signing into the Visitor Portal app:
Invalid command line input. Registration-simply command line flag (-r) can only be used when partner direction is enabled in Intune. Please contact your IT admin.
This volition occur if Intune integration is turned off. The Jamf Pro server sends a pulse to the Intune servers when this is unchecked, telling Intune that the integration is disabled. To resolve this issue, re-enable Intune integration in Jamf Pro
When trying to register a Jamf enrolled device with Intune via Jamf Self Service, the Company Portal does non launch and the following mistake is generated:
The operation couldn't be completed. (Com.jamfsoftware.task.errors 1.) [com.jamfsoftware.task.errors lawmaking=one}
This occurs if the user shell for your macOS user account is non prepare to a working directory such equally /bin/bash. Fix the user shell for your user business relationship to a working directory to resolve the issue.
Shonda Hodge
Intune Support Engineer
Microsoft
Web log Postal service Updates:
iii/26: Update to the "Device bank check-in and compliance" section to clarify that if a device is marked every bit unresponsive in Jamf, it will not bear upon the compliance status of a device in Intune. However, if a device is retired in Jamf, Intune volition reevaluate the compliance state of the device.
Source: https://techcommunity.microsoft.com/t5/intune-customer-success/support-tip-troubleshooting-issues-with-macos-devices-when-using/ba-p/462912
0 Response to "Alexa I Encountered an Error When Trying Reach Salesforce Please Try Again Later"
Postar um comentário